-
Secure Random Key Generation Algorithm카테고리 없음 2020. 9. 2. 05:26

This class provides a cryptographically strong random number generator (RNG).
Sep 13, 2013 The obvious question to ask is. Why mess with random number generation? The answer is rather simple: good random numbers are fundemental to almost all secure computer systems. Without them everything from Second World War ciphers like Lorenz to the SSL your browser uses to secure web traffic are in serious trouble.
Random Key Generation In Cryptography
A cryptographically strong random number minimally complies with the statistical random number generator tests specified in FIPS 140-2, Security Requirements for Cryptographic Modules, section 4.9.1. Additionally, SecureRandom must produce non-deterministic output. Therefore any seed material passed to a SecureRandom object must be unpredictable, and all SecureRandom output sequences must be cryptographically strong, as described in RFC 1750: Randomness Recommendations for Security.
A caller obtains a SecureRandom instance via the no-argument constructor or one of the
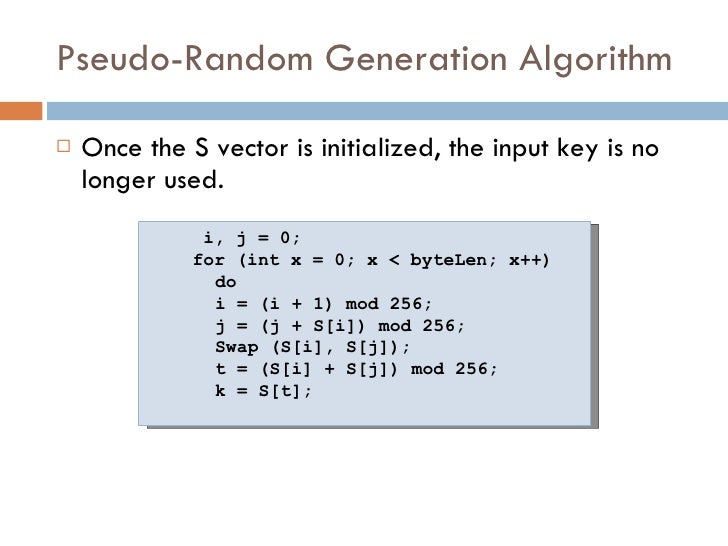
getInstancemethods:Many SecureRandom implementations are in the form of a pseudo-random number generator (PRNG), which means they use a deterministic algorithm to produce a pseudo-random sequence from a true random seed. Other implementations may produce true random numbers, and yet others may use a combination of both techniques.
Typical callers of SecureRandom invoke the following methods to retrieve random bytes:
Secure Random Key Generation Algorithm Free
Callers may also invoke the
generateSeedmethod to generate a given number of seed bytes (to seed other random number generators, for example): Note: Depending on the implementation, thegenerateSeedandnextBytesmethods may block as entropy is being gathered, for example, if they need to read from /dev/random on various Unix-like operating systems.